Managing your vendor security process is a critical component of the SaaS management lifecycle. Yet many Infosec teams struggle to properly maintain this process due to limited tools, competing priorities, time constraints, or the absence of an established workflow.
Being proactive about your vendor security review process isn't just good practice—it's essential for preventing costly data breaches and security vulnerabilities.
In 2020 alone, there were nearly 1,001 recorded data breaches across all industries in the US. Giants with virtually unlimited resources like Zoom and Microsoft have been victims of data breaches. Most recently, over 500,000 Zoom users had their personal data on the dark web. You can probably see where I’m going with this. That pales in comparison to the more than 280 million Microsoft customer records that were left unprotected online. If it can happen to them, it can happen to anyone.
The point? Maintain a very thorough and robust vendor security review process!
Before we dive into how you can use Jira to manage your vendor security review process, here are a few more salient reasons to consider having one.
Why do you need vendor security management?
More than 60% of data breaches are because of third-party vendors. Therefore, vendor security management is crucial for the long-term success of your SaaS tools, especially as your company grows.
As your SaaS tools grow, so do the potential problems that can come with third-party vendors of IT products and other tools. As a SaaS manager, you must stay compliant and protect data for both your business and your customers.
As they say, you can’t fix what you don’t track. A vendor security review process ensures that invisible vulnerable areas that are prone to data breaches are brought to the surface and dealt with before they become a problem.
This proactive effort now will save more money on data breaches that could have been avoided.
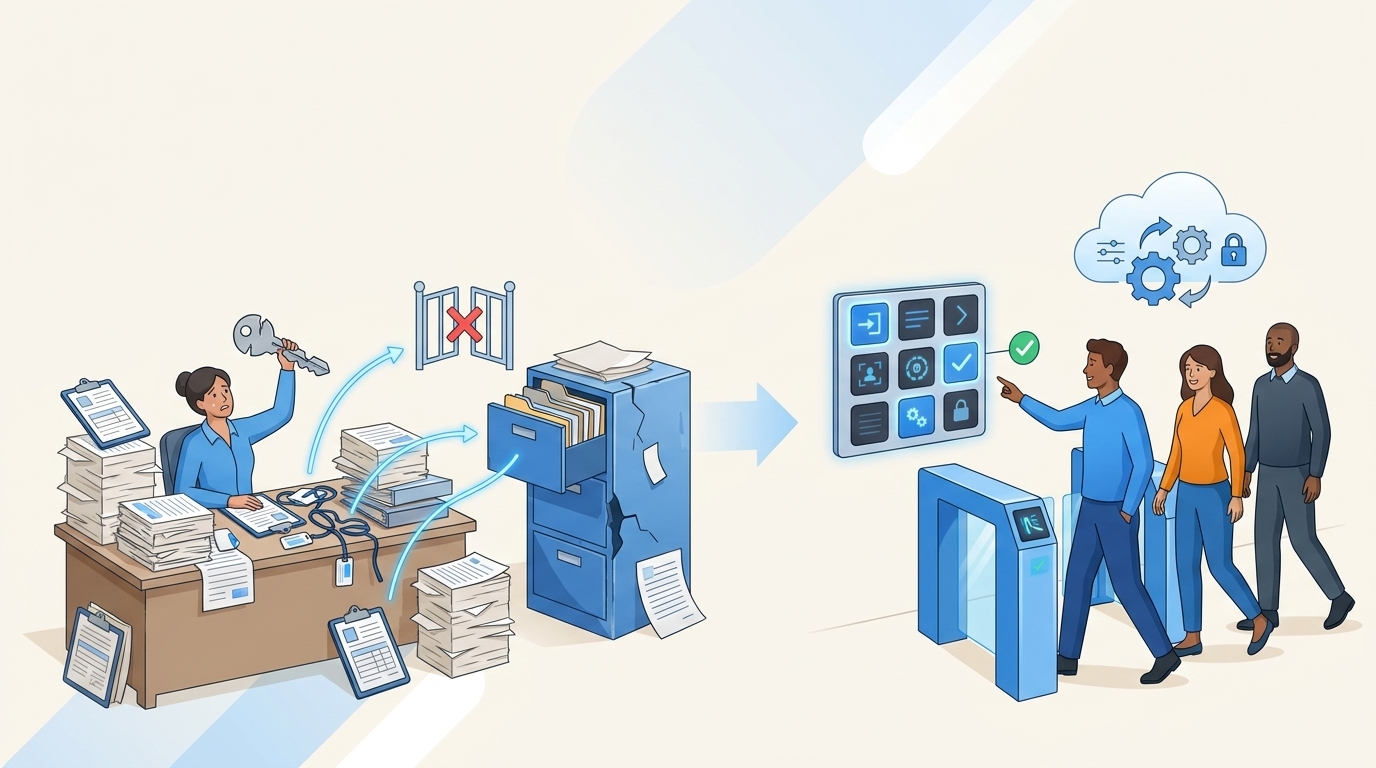
The Pain of Manual Vendor Security Reviews
For many organizations, the vendor security review process is entirely manual and incredibly time-consuming. If this sounds familiar, you're not alone. The typical workflow often looks like this:
A new vendor request comes in through a service desk ticket. Then infosec or IT emails out a questionnaire, which can be anywhere from 100-150 questions. The vendor either completes it or, as often happens, refuses and instead sends their own documentation like SOC2 reports or security policies.
Then comes the truly painful part: someone on your team has to manually review all this information, validate responses, and extract the relevant details from lengthy documents. This process can take a sometimes up to 10 hours per vendor. For companies dealing with hundreds of suppliers, this quickly becomes unmanageable.
As one compliance professional put it: "The entire process is painful. Getting the information back from suppliers is difficult and takes a long time. They don't always fully answer the questions or give us what we ask for. And then when we do get it back, it's an insane amount of stuff to review."
With teams constantly bringing in new vendors and the need to regularly review existing ones, many IT teams simply don't have enough man-hours to keep up.
How to Use AI Vendor Risk Management for Jira to Automate Your Security Review Process
Our AI-powered Vendor Risk Management app for Jira transforms how IT security teams manage third-party risk directly within Jira. Here's how to implement it in your workflow:
1. Vendor Intake and Initial Risk Assessment
The process begins when a new vendor request comes in through your Jira service desk. Simply add the label "securityreview" to the ticket, and our app automatically pulls it into the vendor management dashboard.
The app immediately provides context about the supplier and performs an initial risk assessment based on the information available. For example, if a vendor has access to internal systems, it might be flagged as "high risk." You can adjust these risk levels as needed based on your organization's criteria.

This initial assessment helps you prioritize which vendors need the most thorough review, allowing you to focus your resources where they matter most.
2. Automated Questionnaire Analysis
This is where the real magic happens. Our AI can analyze vendor documentation like SOC2 reports, DPAs, and security policies that were attached to the Jira ticket to automatically extract answers to your security questionnaire.
The system cites sources and provides a confidence score for each answer, helping you identify which responses need further verification.

For each AI-generated answer, you have three options:
- Accept the answer if it meets your requirements
- Flag it for further review if you need to investigate
- Request vendor input if the AI couldn't find sufficient information
This automated analysis can reduce review time by up to 75%, turning what was once a 10-hour process into something that can be completed in just a couple of hours.
3. Streamlined Vendor Communication
For questions that need vendor input, our app makes it easy to collect the necessary information:
Select the questions that need vendor input and click "Send to Vendor." The system generates a customized email with a link to a form where the vendor can provide their answers.
The vendor receives a professional, branded email with clear instructions on what information you need. They can fill out the form online and even attach supporting documentation directly.
Once the vendor submits their responses, the answers are automatically populated back into your questionnaire in Jira, with a clear "Answered by Vendor" flag. You'll receive a notification when the vendor has completed the questionnaire.
This eliminates the back-and-forth email exchanges that typically slow down the vendor review process.
4. Comprehensive Review and Approval
After all questions have been answered—either by the AI or the vendor—you can review the complete questionnaire within Jira.
You can go through each response and mark it as accepted once you're satisfied with the answer.
The system tracks your progress, showing how many questions have been reviewed and accepted.
Once all questions are accepted, the vendor's status automatically changes to "Completed."
You can then mark the vendor as "Approved" in the system, creating a clear audit trail of your security review process.
All documentation and questionnaire responses are stored in one centralized location, making it easy to reference during future reviews or audits.
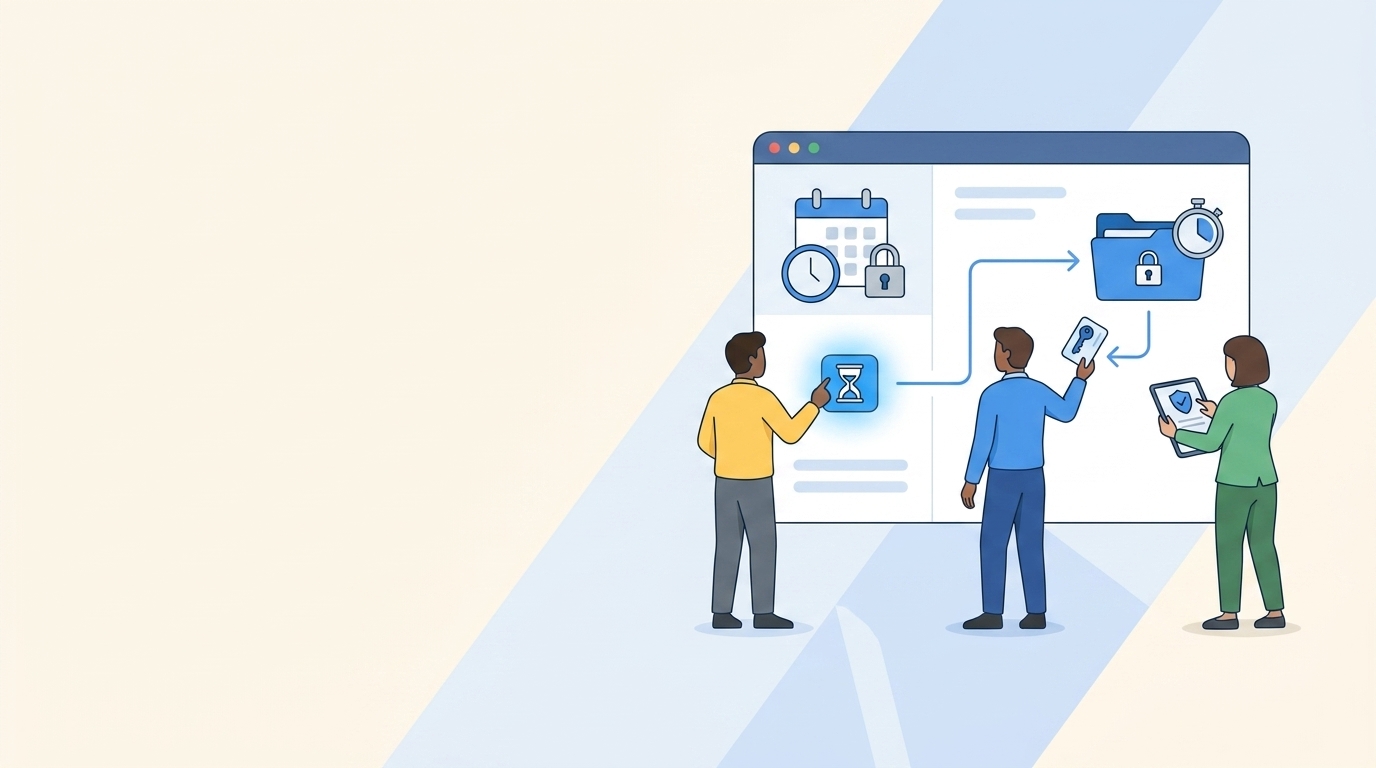
5. Ongoing Vendor Management
The app provides a dashboard view of all your vendors, allowing you to:
- See at a glance which vendors are pending review, in progress, or approved
- Track when each vendor was last reviewed
- Schedule automatic reminders for annual reviews
- Monitor the risk level of each vendor in your portfolio
This gives you complete visibility into your vendor security posture and helps ensure nothing falls through the cracks.
Real-World Benefits of Automating Your Vendor Security Review Process
Organizations using AI Vendor Risk Management for Jira have reported significant improvements in their security review processes:
Time Savings: What once took 10+ hours per vendor now takes just 2-3 hours, freeing up valuable time for your security team to focus on more strategic initiatives.
Increased Throughput: Teams can process 3-5 times more vendor reviews with the same resources, helping clear backlogs and ensure all vendors are properly assessed.
Better Vendor Experience: Vendors appreciate the streamlined process and clear communication, leading to faster responses and better cooperation.
Improved Compliance: With a consistent, documented process for all vendor reviews, you can easily demonstrate compliance with regulations and internal policies.
Reduced Risk: By ensuring all vendors are thoroughly reviewed, you can identify and mitigate security risks before they lead to data breaches.
Getting Started with AI Vendor Risk Management for Jira
Ready to transform your vendor security review process? Here's how to get started:
- Install the AI Vendor Risk Management app from the Atlassian Marketplace
- Upload your custom security questionnaire or use our template
- Add the "securityreview" label to your vendor intake Jira tickets
- Start automating your vendor security reviews!
The app is designed to work seamlessly with your existing Jira workflow, requiring minimal setup and training. And as your needs evolve, our team is continuously adding new features based on customer feedback.
Conclusion
Managing your vendor security review process doesn't have to be a manual, time-consuming task. With AI Vendor Risk Management for Jira, you can automate the most tedious parts of the process while maintaining the thorough security standards your organization requires.
By streamlining vendor intake, automating questionnaire analysis, simplifying vendor communication, and providing comprehensive oversight of your vendor security posture, our app helps you protect your organization from the 60% of data breaches that originate with third-party vendors.
In today's rapidly evolving security landscape, having a robust, efficient vendor security review process isn't just good practice—it's essential for protecting your business and your customers. AI Vendor Risk Management for Jira gives you the tools you need to make that process as painless and effective as possible.
Ready to see how it works for yourself? Try AI Vendor Risk Management for Jira today and transform how you manage vendor security reviews.