83% of employees say workplace technology shapes how they feel about work, yet most IT teams still make access feel like a scavenger hunt through tickets, Slack threads, and follow-up pings. If you're trying to create an effective employee experience while tightening access control, that split is probably the thing breaking both.
Creating effective employee experience usually gets framed as an HR or manager problem. I don't buy that. A huge chunk of it is access. Day one access. Same-day access. Time-bound access when someone needs elevated rights for one hour, not forever. And if that process is broken, people feel it immediately.
Key Takeaways:
- Creating effective employee experience starts with fast, predictable access to the tools people need to do their jobs.
- The real bottleneck isn't policy. It's the split between Jira, Slack, your identity provider, and spreadsheet-based evidence.
- If elevated access doesn't expire automatically, least privilege usually turns into standing privilege.
- A simple rule works well: if access is temporary by nature, make the entitlement temporary by default.
- Teams that provision through the identity provider create cleaner audits because the change is authoritative and traceable.
- Strong employee experience and strong governance are not tradeoffs when the workflow is designed right.
- Learn more about Multiplier
Why creating effective employee experience often fails at the access layer
Creating effective employee experience fails when access is treated like admin cleanup instead of core infrastructure. Employees don't experience your policy deck. They experience waiting, ambiguity, and whether they can actually do their job at 9:07 a.m. on Monday.
A lot of teams still think the employee experience problem lives in culture surveys, better onboarding docs, or cleaner request forms. Those matter. But the hidden problem is operational. The ITSM-IGA split creates friction everywhere. Jira handles intake. Slack handles nudges. The identity provider handles the real change. Then someone rebuilds evidence later for audit. That's four systems for one moment that should feel simple to the employee.
Picture a new hire at a 400-person company. They start at 8:30. Laptop works. Slack works. Then they realize they don't have access to the product analytics tool, the CRM sandbox, and one shared folder they need for training. They submit one request in Jira, message IT in Slack for another, and mention the third in a manager thread because they're not sure what the right process is. By noon, nobody knows which request is canonical. That's not just messy. It tells the employee your company is making them earn basic productivity.
I've seen this movie before. Once headcount starts climbing, manual access work compounds fast. One high-growth AI company ended up processing 3,800 plus access requests in a year, and 75% of them became fully automated after they cleaned up the workflow. That's the interesting part. The issue wasn't demand. The issue was the system around the demand.
There's a case to be made for separate governance tooling if you're a huge enterprise with very specialized requirements. Fair enough. But for most mid-market teams already living in Atlassian, a separate portal often adds one more place for work to stall. That extra layer doesn't feel like governance to employees. It feels like delay. And delay is one of the fastest ways to ruin employee experience before the person has even settled into the role.
So the question isn't whether access matters to employee experience. It obviously does. The real question is why teams keep designing access like an audit workflow instead of a work workflow.
The real issue is standing privilege, not slow approvals
Creating effective employee experience gets better when you stop optimizing for permanent access and start optimizing for fast, controlled access. That's a different mindset. And it changes almost everything.
The Access Window Rule changes how teams think
The Access Window Rule is simple: if a permission is only needed for a task, incident, or short-term project, the access window should match the work window. One hour. Six hours. Twenty-four hours. Not indefinite "for convenience."

Most teams don't do this. They grant broad access because it's easier operationally. Then months later, nobody remembers why someone still has admin rights, or why a contractor still has access to a sensitive app. The original shortcut becomes long-lived risk. That's why policy-heavy least privilege often fails in practice. The policy says one thing. The workflow does another.
Security teams know this already. The problem is they often try to solve it with approvals alone. But approvals without expiry just create approved standing privilege. That's not least privilege. That's documented overprovisioning.
A fintech team dealing with sensitive customer data figured this out the practical way. They reduced privileged access by 85% once they made just-in-time access part of the operating model instead of an exception process. More than 1,300 access requests were automatically revoked after approved windows ended. That number matters because it shows the mechanism. Not awareness. Enforcement.
Fast access and least privilege are only opposites in bad systems
A lot of people assume tighter controls make employee experience worse. I get why. In bad systems, they do.

If every elevated request means a long form, two reminders, a manual group change, and a cleanup task nobody owns, then yes, governance feels painful. But that's a process flaw, not a law of nature. In a well-built setup, you can approve quickly, provision quickly, and revoke automatically when time runs out.
This is where the old argument breaks down. Some teams still operate like the only choice is broad standing access or constant ticket backlog. That's the wrong frame. The better frame is this: can your workflow issue access fast enough that people don't need permanent entitlements in the first place?
If the answer is no, you'll keep overprovisioning to protect productivity. If the answer is yes, you can finally create effective employee experience without absorbing avoidable risk. That's the pivot.
Authoritative provisioning beats screenshot-based governance
Provision through your identity provider. That's the rule. If the change happens there, it's authoritative, reversible, and easier to audit.
The alternative is what a lot of teams still do. A Jira issue gets approved. Someone checks Slack. Someone logs into Okta or Entra. Someone adds a user to the right group. Then someone pastes a comment or screenshot into the ticket so there's some record later. It works, technically. But it does not hold up well under scale.
One crypto company grew by 32% in eight months and was onboarding hundreds of people while dealing with access requests across Slack, email, and Jira. Their IT team was manually chasing approvals and logging into Okta to make group assignments. That's the kind of workflow that eats your day in 15-minute chunks. Death by admin.
And that admin cost hits employee experience too. Because while IT is juggling side-channel work, employees are waiting. Or pinging. Or being granted overly broad access so nobody has to deal with the request twice. Broken systems create bad incentives. That's the real issue. The next step is building an access model that fixes both speed and control.
What creating effective employee experience looks like in practice
Creating effective employee experience through access governance means the employee sees one clear path, the approver sees one clear decision, and IT doesn't have to reconstruct the truth later. That's the operating model. Simple on the surface. Very disciplined underneath.
Start with the employee-facing path, not the policy doc
A good access system starts where the employee starts. They need something. They should know where to request it. They should understand what role to choose. And they should trust the request won't disappear into a black hole.
That sounds obvious, but it's rare. A lot of companies still let access requests arrive through email, Slack, hallway messages, onboarding spreadsheets, and random Jira issue types. Then they wonder why the employee experience feels inconsistent. Because it is inconsistent. You gave people five front doors and no map.
The practical fix is a single intake path with sanctioned apps, clear roles, and the right context upfront. That's why I like the Storefront-to-Group model: employees choose from a clear app catalog, roles map to identity provider groups, and the request enters a workflow that actually knows what to do next. Less guessing. Fewer back-and-forth messages. Better employee experience right away.
A company scaling from 100 to 500 employees described Tuesdays like groundhog day because new hires would trigger a flood of access asks the day after starting. The team didn't have enough information to act, and ownership was muddy. That's a design flaw, not a staffing flaw. Once the request path gets standardized, the noise drops.
Use the 3-Gate model for approval design
You don't need a giant approval maze. You need three gates and clarity on when each applies. I think of it as the 3-Gate model.
- Auto-approve for low-risk, common access.
- Single approver for normal business access.
- Time-bound approval for elevated or sensitive access.
That's it. Keep the model tight.
If every app gets the same approval treatment, your system gets slow fast. If nothing requires approval, your controls are weak. The middle ground is conditional routing. Low-risk requests move fast. Sensitive requests go to the manager, app owner, or another specific approver. Temporary elevated rights get extra guardrails with explicit duration.
Some people will argue for more layers because more layers feel safer. I understand the instinct. But extra approval hops often create the illusion of control while making the workflow brittle. What you actually want is decision quality plus enforcement. If an app is risky, add time bounds. If it's routine, don't make people fight through a maze.
And the employee feels this immediately. When the approval design matches the actual risk, creating effective employee experience stops being abstract. The process just feels fair. Fast when it should be fast. Controlled when it should be controlled.
Make expiry automatic or don't pretend it's least privilege
This is the point a lot of teams avoid because it's the hard operational part. Least privilege is only real when removal happens without heroics.
If you rely on someone remembering to revoke access later, the access usually sticks. Maybe not every time. But often enough that it becomes the norm. That's why the Expiry-or-Exception rule matters: every elevated entitlement should either expire automatically or require a documented exception with an owner.
Honestly, this is where a lot of governance programs quietly fail. The policies look clean. The reviews look serious. But the real environment still has leftover access everywhere because nobody built revocation into the workflow. So the organization feels governed while carrying unnecessary standing privilege.
The better design is straightforward. Request the access. Approve it. Provision it through the identity provider. Start the clock. Remove it at expiry. Record the whole thing on the originating record. That is both a better security model and a better employee experience model because people can ask for what they need without triggering a permanent access decision.
Review based on usage, not memory
Quarterly reviews are where employee experience and governance often both go sideways. Managers get a spreadsheet dump. App owners rubber-stamp. IT follows up later. Nobody loves it.
The better way is usage-aware review. If a person hasn't logged in for 90 days, that should shape the recommendation. If a reviewer can see the user, group, department, and last login in one place, decisions get faster and better. The Memory-to-Evidence Shift matters here. Reviewers should not have to remember whether access still makes sense. The workflow should show enough context to make the call.
And this affects employee experience more than people think. Bloated access environments create confusion. People keep tools they don't use, lose track of what they actually have, and sometimes inherit access that doesn't match their role anymore. Clean access is not just cleaner for auditors. It's cleaner for employees too.
Use one maturity test before you automate further
You don't need to automate everything on day one. But you do need to know whether you're ready.
I use a simple maturity test:
- Can employees request access through one standard path?
- Are roles mapped to identity provider groups?
- Does each app have a named approver model?
- Can elevated access be time-bound?
- Can revoked access be evidenced without screenshots?
If you answer no to three or more, don't chase fancy policy architecture yet. Fix the operating basics first. If you answer yes to four or five, you're ready to push much harder into automation.
That's the part people skip. They want the advanced governance posture before they have clean plumbing. But creating effective employee experience and effective governance both depend on the same boring foundations. Clean intake. Clear roles. Authoritative provisioning. Automatic expiry. Usable reviews. Not glamorous. Very effective.
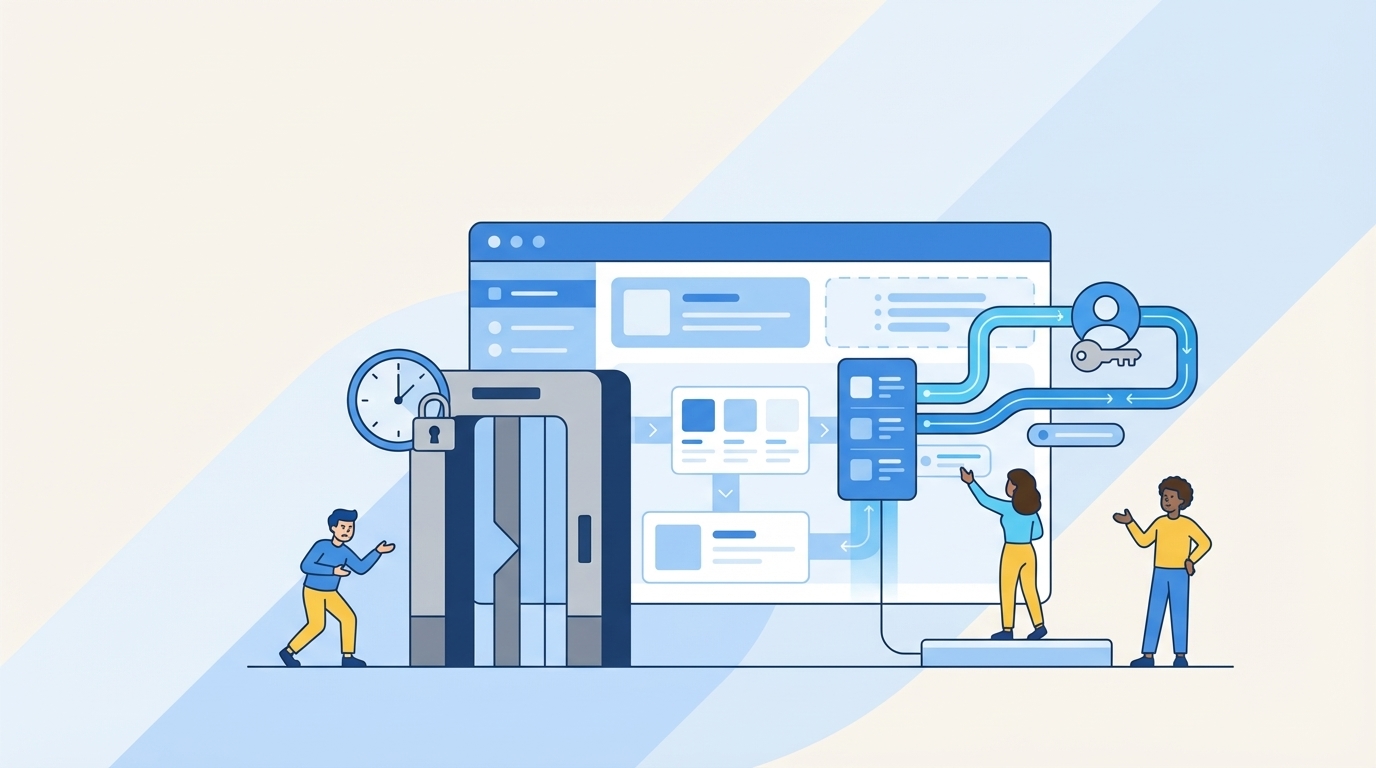
How Multiplier makes this model operational inside Jira
Multiplier turns the access model above into something teams can actually run inside Jira Service Management. That's the important distinction. Not a separate theory layer. An operating layer.
Multiplier ties requests, approvals, and provisioning to one record
Multiplier gives employees a Jira-native Application Catalog, also available through Slack, so access starts from one standard request path instead of five improvised ones. Apps can be shown as approved catalog items, roles map to identity provider groups, and the request creates a Jira issue that becomes the system of record.

From there, Multiplier handles Approval Workflows inside Jira and Slack. Admins can route decisions to a manager, app owner, or specific user based on the app. Once a request reaches the approved state, Multiplier can trigger Automated Provisioning through identity provider groups in Okta, Entra ID, or Google Workspace. That matters because the change happens through the authoritative identity layer, not through side-channel admin work.
This is where the employee experience lift shows up. The person requests access in a familiar place. The approver acts in a familiar place. IT isn't manually re-keying entitlements. And the Jira issue captures what happened as it happened.
Multiplier makes time-bound access real, not aspirational
The strongest part of the model, in my view, is Time-Based Access. Requesters can choose a duration like 1, 6, or 24 hours during submission. After approval, Multiplier adds the user to the mapped identity provider group, starts the timer, and removes the membership when the window expires. The revocation is recorded back to Jira.
That closes the gap most teams never close. They want just-in-time access, but they don't have operational enforcement. Multiplier gives them the enforcement path. If access is provisioned via identity provider group membership, expiry can be automatic. If it's purely manual or outside that flow, it can't. That boundary matters, and it's worth being direct about it.
Multiplier also supports Access Reviews in JSM, where reviewers can see user attributes, groups, last login, and recommendations before marking Keep or Revoke. And for teams focused on unused licenses, Auto Reclaim can use identity provider login telemetry, inactivity thresholds, grace periods, and exclusions to remove unused access and create a Jira ticket documenting the change. Different workflows. Same principle. Governance happens in the work system, and evidence is produced as part of the work.
If you want to create effective employee experience without accepting standing privilege as the tradeoff, that's the model. And if you want to see what that looks like in your own environment, Get started with Multiplier.
Creating effective employee experience starts with better access design
Creating effective employee experience is not just about culture, perks, or better onboarding messaging. It's about whether people can get the right access fast, whether elevated access expires when the work is done, and whether IT can support growth without drowning in manual admin.
Most teams don't have a people problem here. They have a workflow problem.
Fix the workflow, and a lot changes. Employees get moving faster. Security gets less standing privilege. Audits get easier because evidence is already there. And IT stops spending half the week stitching together approvals, screenshots, and cleanup tasks from disconnected systems.
That's why this category matters. Not because governance got more theoretical. Because it finally got operational.
Frequently Asked Questions
How do I set up time-bound access for new hires?
To set up time-bound access for new hires using Multiplier, follow these steps: 1) When a new hire requests access through the Jira Service Management (JSM) portal, they can select the duration of access needed (like 1, 6, or 24 hours). 2) After the request is approved, Multiplier automatically provisions access and sets a timer to revoke it when the time expires. 3) Ensure that the applications are configured to support time-based access for this feature to work effectively. This way, you minimize standing privileges and ensure that access is only granted when necessary.
What if I need to revoke access quickly?
If you need to revoke access quickly, you can use Multiplier's automated provisioning feature. Once access is no longer required, simply update the Jira ticket associated with the access request. Multiplier will then communicate with your identity provider to remove the user from the relevant group. This process is efficient and ensures that the revocation is logged for audit purposes, maintaining a clean record of access changes.
Can I customize the approval workflow for specific applications?
Yes, you can customize the approval workflow for specific applications in Multiplier. To do this, go to your JSM settings and map the application to the desired approvers, which can include app owners or managers. You can set default approvers globally and override them on a per-app basis. This flexibility allows you to ensure that the right people are involved in the approval process, streamlining access requests and enhancing governance.
When should I conduct access reviews?
You should conduct access reviews regularly, typically on a quarterly basis, to ensure that user access remains appropriate. With Multiplier's Access Review feature, you can create campaigns that allow reviewers to see user attributes, last login dates, and recommendations for revocation. This helps keep your access environment clean and ensures compliance with governance policies. Make sure to include only approved applications in your review campaigns for a streamlined process.
Why does my team need an application catalog?
An application catalog is essential because it simplifies the access request process for employees. With Multiplier's Jira-native Application Catalog, employees can browse approved applications and submit requests in one place, reducing confusion and improving efficiency. This centralized approach also helps IT maintain control over access requests and ensures that all requests are documented for audit purposes, making it easier to manage user access and compliance.
Multiplier connects to your existing JSM setup in minutes. Try it free on the Atlassian Marketplace.



![Centralized Workflows for Faster Access Management [2026]](https://cdn.prod.website-files.com/60cc3b1de50f53117a9c8119/6a0f9eb8ffdd16d3206ab77a_centralized-workflows-for-faster-identity-provisioning-hero-1779408525848.jpeg)




