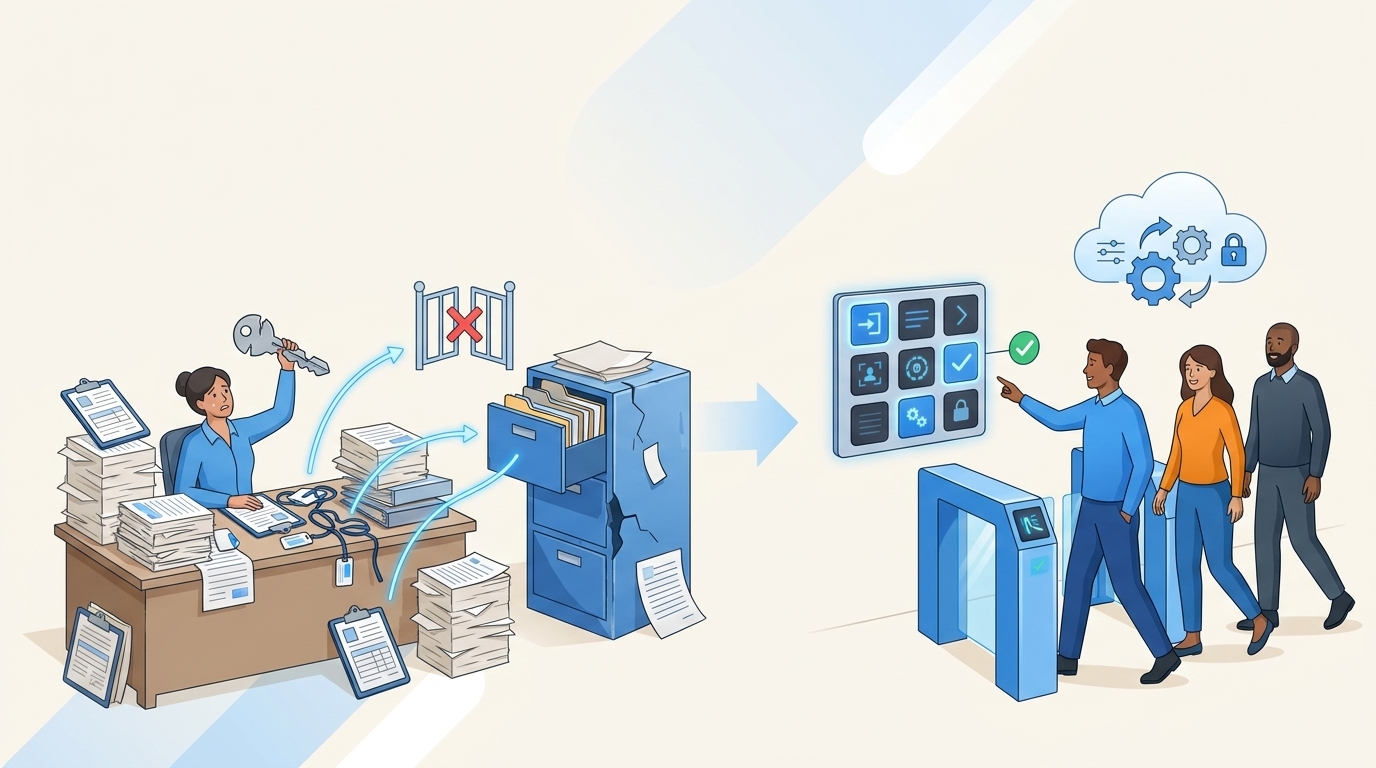
Privilege creep prevention is the elephant in the room for most high-growth IT teams. You start out lean. You give everyone access to everything just to move fast. Then you hit 500 employees. Suddenly, you have marketing managers with admin rights to production databases. You have former contractors still lurking in your AWS instance. Most teams try to fix this by buying a dedicated identity governance portal. They think another tool will solve the problem. They are wrong.
Manual audits are a losing game. If you get a 20 percent response rate on your first access review email, that is amazing. Most people will ignore your requests. Once you understand these ratios in IT, chasing down approvals feels like a real waste of time. The real fix is not another separate tool. You have to figure out the best way to position your governance inside the tools your team already uses.
Key Takeaways:
- Separate identity portals slow down access and create real blind spots for IT teams.
- Standing privileges happen because manual revocation is too painful to execute consistently.
- Time-bound access eliminates the need for constant manual cleanup and prevents credential hoarding.
- Approvals must happen in chat platforms like Slack to avoid the Friday afternoon escalation trap.
- Audit evidence should be a natural byproduct of your ticketing system, not a spreadsheet you build later.
Why Policy-Heavy Privilege Creep Prevention Fails at Scale
Policy-heavy privilege creep prevention fails because it relies on manual enforcement rather than baked-in automation. When IT teams have to manually revoke access or chase down approvals across email and Slack, policies get ignored in favor of speed. This creates real security gaps that only surface during audits.

The Illusion of Annual Certifications
Annual access certifications provide a false sense of security for most organizations. You send out a sprawling spreadsheet to department heads asking them to review hundreds of permissions. The managers are busy. They do not have time to look up what each specific role actually means. So they rubber-stamp the entire list just to get IT off their backs.

This is where the system breaks down. You haven't actually verified anything. You just shifted the liability to a manager who lacks the context to make a good decision. A confused manager never revokes access. They fear breaking a critical workflow, so they leave the permissions active. This guarantees that your attack surface grows larger every single month.
The Disconnect Between ITSM and Identity
The ITSM and identity split is the real bottleneck in modern IT operations. Your employees request access in Jira Service Management. The manager approves the request in an email thread. Then an IT agent logs into Okta to manually assign the user to a group. Finally, someone takes a screenshot of the Okta log and pastes it back into Jira for the auditor.

This fragmented workflow is a disaster for productivity. It forces your IT team to act as human routers between disconnected systems. Every time you split the work between tools, you pay a hidden tax in context switching. Tickets bounce around. Approvals stall. Evidence gets lost in the shuffle.
The Real Cost of Overprovisioned Access
Overprovisioned access costs organizations thousands in unused SaaS licenses and creates massive security vulnerabilities that compound daily. When we actually look at the data, the financial and operational bleed from unmanaged entitlements is staggering. It is not just a compliance issue. It is a real drag on your bottom line.
Think about the sheer volume of routine requests. IT teams routinely spend 15 hours a week just chasing approvals and provisioning basic software. We worked with one fintech company that experienced an 80 percent reduction in IT workload just by automating these basic steps. Compromised credentials remain the leading cause of security incidents globally. According to the IBM Cost of a Data Breach report, incidents involving stolen credentials take the longest to identify and contain. When everyone has access, no one is secure.
The Friday Afternoon Escalation Trap
Chasing access approvals drains the morale of IT teams who spend their days acting as copy-paste machines instead of engineers. It is exhausting to constantly ping managers on Slack just to get a simple software request pushed through. You end up feeling like a glorified hall monitor.
Picture this scenario. It is 4:00 PM on a Friday. A new engineer needs production access to push a critical hotfix. The approval is stuck in the inbox of a director who is currently on a flight. The engineer escalates to the VP. The VP yells at IT to just grant the access and figure out the paperwork later. You grant the access. You forget to remove it on Monday. Now you have another standing privilege that will sit there until your next audit.
How High-Growth Teams Build Automation-First Access Governance
High-growth teams build automation-first access governance by embedding request and approval workflows directly into their existing service desk. Instead of forcing users into a separate identity portal, they bring the controls to the tools employees already use. This ensures every request is tracked and executed automatically.
Centralize the Request Experience
You need to stop treating access requests like custom IT projects. When employees have to guess how to ask for software, they default to sending direct messages to your IT staff. This bypasses your entire governance structure. The fix is creating a consumer-like storefront for your enterprise applications.
You stand up a self-service catalog directly inside your ticketing system. Employees browse sanctioned applications as tiles with logos. They select the exact role they need. The system captures all the required context up front. This eliminates the back-and-forth clarification emails that delay provisioning. When you make the right way the easiest way, compliance happens naturally.
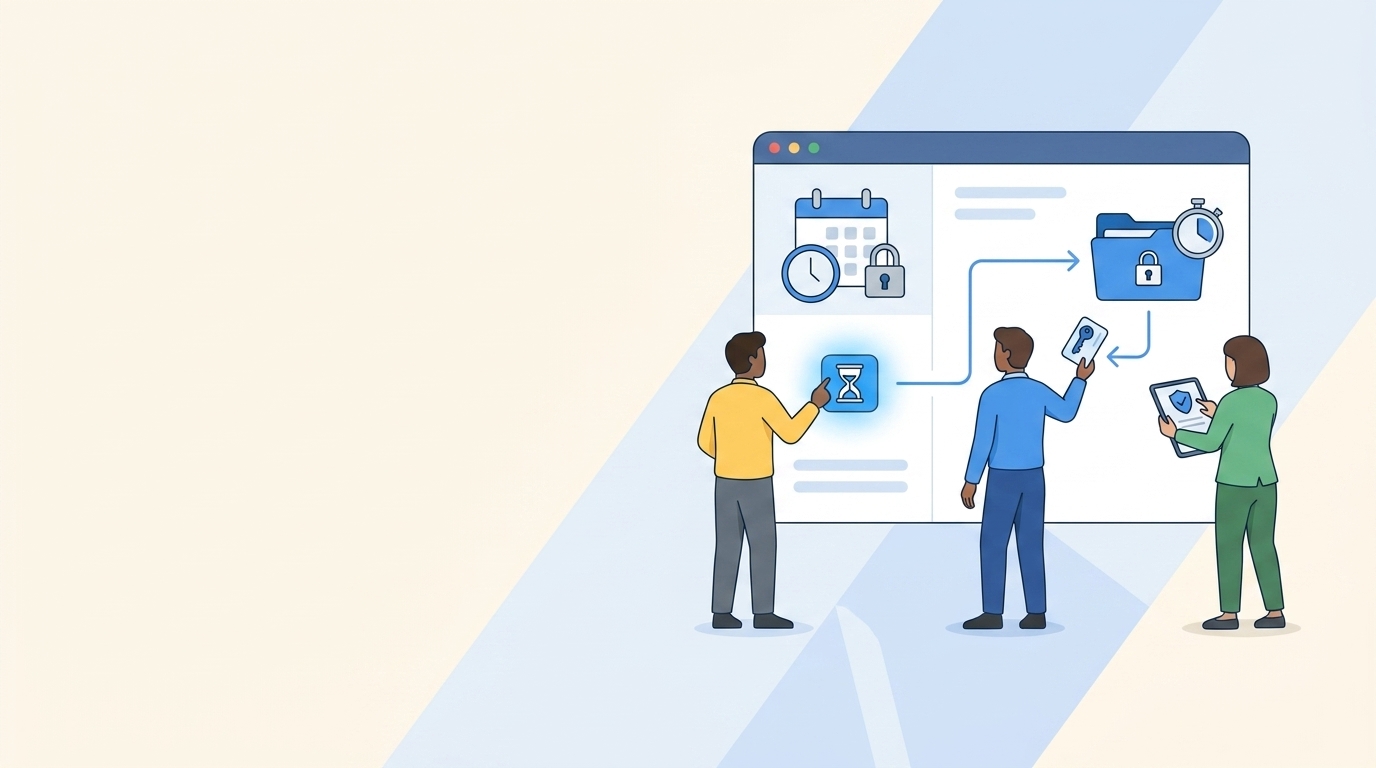
Enforce Time-Bound Access by Default
Time-bound access enforces least privilege by making elevated permissions temporary by default. You grant the access for a specific window of time, and the system automatically revokes it when the timer expires. No human follow-up is required.
Most people will not need permanent admin rights. They just need to run a script or fix a bug. By forcing users to select a duration during the initial request, you eliminate the root cause of standing privileges. The access disappears the moment the job is done. This shrinks your exposure window for production systems and completely changes your security posture.
Shift Approvals to Where Work Happens
Approval workflows only work if they meet managers where they actually spend their time. If you force a sales director to log into a legacy identity portal to approve a Zoom license, they will ignore it. You have to bring the approval to their chat window.
Top performing teams route access decisions directly to Slack. The manager gets a direct message with the context of the request and a simple button to approve or deny. They make the decision in two seconds without leaving their workflow. Fast approvals mean fast provisioning. This eliminates the friction that causes employees to hoard access in the first place.
Make Audits a Byproduct of Normal Work
Audits should be ready by design in your ticketing system, not rebuilt in spreadsheets at the end of the quarter. When you rely on screenshots and manual log exports, you are just asking for compliance failures. You need a system where the evidence writes itself.
When governance lives in your service desk, every action is tied to the originating ticket. The request, the manager's approval, the automated provisioning step, and the eventual revocation all live on a single timeline. If an auditor asks why a developer had access to a database in November, you just hand them the ticket. The proof is undeniable and requires zero prep work from your team.
According to Gartner research on identity governance, organizations that integrate governance directly into their core operational workflows see significantly faster audit resolution times.
Automate License Reclamation Based on Usage
Automating license reclamation cuts SaaS waste by identifying inactive users and pulling their access based on real login data. You stop paying for software that your employees abandoned six months ago.
You set a baseline policy. If a user does not log into a specific application for 30 days, the system sends them a warning. If they still do not log in after a short grace period, the system automatically revokes the license and logs the change in a ticket. You operationalize your cost savings without running a single manual report.
How Multiplier Automates Least Privilege in Jira
Multiplier automates least privilege by embedding identity governance directly into Jira Service Management and Slack. It connects your service desk to your identity provider, standardizing access requests and automating provisioning where roles are mapped to identity provider groups. This reduces standing privileges while keeping audit evidence in one place.
The Jira-Native Application Catalog
The Application Catalog replaces messy Slack requests with a single self-service storefront right inside Jira Service Management. Employees browse sanctioned applications, select their required role, and submit the request. Multiplier syncs these apps and groups directly from Okta, Entra ID, or Google Workspace.
This means your IT team does not have to maintain parallel lists of software. Only approved applications appear in the catalog. Each role maps deterministically to an identity provider group. When the request is approved, Multiplier can provision access automatically through the identity provider for mapped apps and roles. You get a consumer-grade experience for your employees and strong tracking for your auditors.
Time-Based Access and Auto-Revocation
Time-Based Access removes the manual burden of cleaning up elevated permissions. When an employee requests sensitive access, they choose a duration right in the Jira portal. Multiplier provisions the access upon approval and starts a countdown timer.

When that timer expires, Multiplier calls your identity provider to remove the user from the group and logs the change to the Jira issue. Your security team gets the confidence that standing privileges are minimized. Your IT team gets their Friday afternoons back.
Continuous Access Reviews in JSM
Access Reviews replace those massive, error-prone spreadsheets with a streamlined campaign workflow inside Jira. Admins select the applications in scope and assign the appropriate reviewers. The reviewers get a clean dashboard showing user attributes, last login dates, and clear recommendations on who to keep or revoke.
When a reviewer clicks revoke, Multiplier executes the removal automatically in your identity provider. It creates a Jira ticket documenting the change. You get faster review cycles, less rubber-stamping, and completely exportable evidence that is ready for your next compliance audit.
The Path Forward for Identity Operations
The path forward for identity operations requires bridging the gap between ticketing and provisioning. You cannot scale a high-growth company by throwing more IT headcount at manual access requests. The math simply does not work.
You have to lean into automation. You have to put the governance controls exactly where your employees already work. When you unify your service desk with your identity provider, you stop playing defense. You stop chasing approvals and rebuilding audit trails from scratch. You finally get to run a lean, secure operation that actually accelerates the business instead of slowing it down.
Frequently Asked Questions
How do I set up time-based access with Multiplier?
To set up time-based access using Multiplier, follow these steps: 1) When an employee submits a request through the Jira Service Management portal or Slack, they should select the duration for access (e.g., 1 hour, 24 hours). 2) After the request is approved, Multiplier will provision the access and automatically set a timer to revoke it once the duration expires. 3) Ensure that the access is provisioned via identity provider groups for the automatic revocation to work. This way, you can minimize standing privileges and enhance security.
What if I need to revoke access urgently?
If you need to revoke access urgently, you can do so through the Jira ticket associated with the access request. Simply locate the ticket, and if the access was provisioned via Multiplier, you can mark the user for revocation. Multiplier will automatically remove the user from the relevant identity provider group, ensuring that access is revoked efficiently. This process keeps your audit trail intact and helps maintain compliance without manual intervention.
Can I automate access reviews with Multiplier?
Yes, you can automate access reviews using Multiplier's Access Review feature. To do this, create a new access review campaign in Jira Service Management. 1) Select the applications you want to include in the review and assign reviewers for each app. 2) Launch the campaign, and reviewers will receive notifications with a dashboard showing user attributes and recommendations. 3) As reviewers mark users to keep or revoke access, Multiplier will automatically execute the changes in your identity provider, streamlining the entire process and reducing the need for manual spreadsheets.
When should I use the Application Catalog?
You should use the Application Catalog when you want to streamline access requests within your organization. It provides a centralized, user-friendly interface where employees can browse approved applications and request access directly through Jira Service Management or Slack. This eliminates confusion and ensures that all requests include the necessary context. Additionally, it helps IT maintain control and auditability over access requests, making it easier to enforce governance and compliance.
Why does access hoarding happen, and how can Multiplier help?
Access hoarding often happens when employees feel they need to retain permissions to perform their jobs effectively, especially in fast-paced environments. Multiplier helps mitigate this by enforcing time-bound access by default. When employees request elevated access, they must select a duration, ensuring that permissions are only active when necessary. This reduces the likelihood of hoarding and keeps your security posture strong by automatically revoking access once it’s no longer needed.